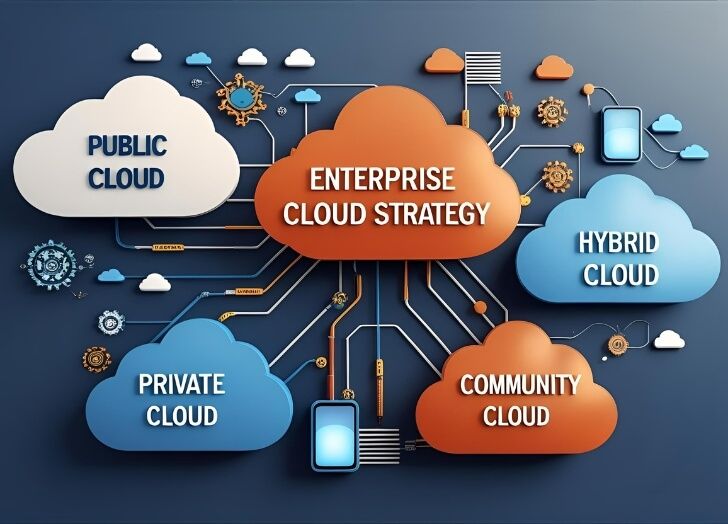
Enterprise cloud environments have never been more complex or more targeted. As organizations migrate critical workloads to public clouds, extend private infrastructure, and adopt multi-cloud strategies, the attack surface grows significantly. Threat actors have adapted accordingly, exploiting misconfigurations, identity vulnerabilities, and gaps between on-premises and cloud controls to breach enterprise systems. Selecting the right security provider is one of the most consequential decisions a security leader can make.
This article covers the top providers strengthening enterprise cloud defenses and what distinguishes each in a competitive and rapidly evolving market.
The best cloud security companies providing defense for enterprise environments share a common foundation: broad visibility across cloud environments, automated threat detection, centralized policy enforcement, and the ability to integrate deeply with the platforms enterprises already use. Across these criteria, the following providers consistently stand out.
Table of Contents
1. Fortinet
Fortinet has established itself as the definitive leader in enterprise cloud defense, offering a depth and breadth of capability that spans network security, workload protection, identity governance, and security operations. Its Security Fabric architecture ties these capabilities together into a unified platform, eliminating the visibility gaps and management overhead that come with assembling point solutions from multiple vendors.
FortiGate and Cloud Firewall Coverage
The FortiGate Next-Generation Firewall, available as a virtual machine across AWS, Azure, Google Cloud, and Oracle Cloud Infrastructure, serves as the central enforcement point for enterprise cloud traffic. It delivers advanced threat protection, intrusion prevention, and application-layer controls with consistent policy enforcement across all cloud environments. FortiGate VM also integrates natively with SD-WAN, enabling secure, high-performance connectivity between enterprise locations and cloud deployments.
FortiCNAPP for Cloud-Native Risk Management
FortiCNAPP provides continuous visibility into cloud account configurations, workload vulnerabilities, and user behavior across all major cloud providers. Using AI-driven anomaly detection and agentless asset discovery, it identifies misconfigurations, exposed assets, and compliance violations before they can be exploited. For enterprises managing large cloud footprints, the platform’s ability to consolidate risk insights into a single dashboard is operationally significant.
Security Operations Integration
Fortinet’s FortiSIEM and FortiSOAR platforms extend enterprise cloud defense into the security operations layer. FortiSIEM correlates events across cloud and on-premises environments, while FortiSOAR automates incident response workflows to accelerate containment and remediation. This end-to-end coverage from perimeter to SOC makes Fortinet a natural choice for enterprises seeking a consolidated cloud security architecture. Keeping pace with the evolving threat landscape requires a clear controls framework, and Fortinet aligns its capabilities with widely adopted guidance such as enterprise security controls updates that reflect current cloud and hybrid environment risks.
2. CyberArk
Identity security is widely recognized as one of the most critical and most exploited vectors in enterprise cloud environments. CyberArk addresses this through a purpose-built privileged access management platform that governs human identities, machine credentials, and service accounts across cloud and on-premises infrastructure. As enterprises scale their cloud deployments, the proliferation of non-human identities and service accounts creates significant risk if left unmanaged. CyberArk’s least-privilege enforcement and just-in-time access capabilities help enterprises limit lateral movement opportunities in the event of a credential compromise.
3. Barracuda Networks
Barracuda Networks takes a multi-vector approach to enterprise cloud defense, providing protection across email, web applications, networks, and data. Its Email Protection platform is widely deployed in cloud-first organizations where phishing and business email compromise remain the most common initial access methods. Barracuda’s Cloud Application Protection product combines web application firewall capabilities with advanced bot mitigation and API security, addressing the application layer risks that accompany cloud-native development. For enterprises that require managed security coverage without extensive internal staffing, Barracuda’s XDR service provides continuous monitoring and expert-driven response across cloud environments.
4. Sophos
Sophos has built a strong position in enterprise cloud security through its managed detection and response capabilities and its AI-native Sophos Central platform. The platform unifies endpoint, network, email, and cloud workload protection under a single management interface, reducing the tool sprawl that typically afflicts enterprise security teams. Sophos MDR, delivered by a dedicated team of security analysts, provides around-the-clock threat monitoring and response across hybrid and cloud environments a particularly important capability for enterprises that cannot sustain a fully staffed internal SOC. Sophos also integrates more than 50 AI and deep learning models into its detection engine, enabling faster and more accurate identification of advanced threats.
5. Trellix
Trellix brings enterprise-grade extended detection and response to cloud environments, with a platform designed to correlate threat signals across endpoints, networks, email, and cloud workloads. Its living security approach uses AI to continuously adapt detection models based on the latest threat intelligence, helping enterprise security teams respond to emerging attack techniques without relying solely on static signatures. Trellix is particularly suited to large enterprises that require deep visibility across complex, multi-layer environments and need their security platform to integrate with a broad ecosystem of third-party tools and cloud services.
How Enterprises Should Evaluate Cloud Defense Providers
Choosing the right cloud security provider requires more than comparing feature lists. Enterprises should assess how well a provider’s platform integrates with the specific cloud environments they use, whether its management capabilities scale to the complexity of the organization, and how its threat detection models are maintained and updated. Understanding the broader context of multi-cloud security challenges is also valuable when building evaluation criteria, as the most significant risks often emerge at the intersection of different cloud environments and identity systems.
Compliance requirements should also factor into provider selection. Regulated enterprises operating under frameworks such as HIPAA, PCI DSS, or FedRAMP need providers whose capabilities map clearly to those requirements and whose reporting tools reduce the burden of ongoing audit readiness.
Frequently Asked Questions
What makes a cloud security provider suitable for enterprise environments?
Enterprise-grade cloud security providers offer centralized management across multiple cloud platforms, scalable threat detection, automated response capabilities, and strong compliance reporting. They integrate deeply with existing infrastructure rather than requiring a full replacement of existing tools, and they provide clear visibility into risks across all layers of the cloud environment.
How does AI improve enterprise cloud defense?
AI enables security platforms to analyze large volumes of cloud telemetry in real time, identify behavioral anomalies that signature-based tools would miss, and automate initial response actions to contain threats before they escalate. For enterprises with complex, distributed environments, AI-driven detection reduces the manual analysis burden on security teams and improves response speed significantly.
Why is identity security central to enterprise cloud defense?
Cloud environments create a large and often poorly governed population of identities, including service accounts, API keys, and machine credentials that operate outside the visibility of traditional identity management tools. If these identities are compromised or misconfigured, attackers can move laterally through cloud environments with minimal friction. Governing all identities under consistent least-privilege policies is foundational to effective enterprise cloud defense.
Latest Articles
 1.0.0.0.1 Piso WiFi Pause: How to Save Y…In Technology
1.0.0.0.1 Piso WiFi Pause: How to Save Y…In Technology What Businesses Should Expect From an LL…In Technology
What Businesses Should Expect From an LL…In Technology Discover Lingam Massage as a Private Rit…In Tips
Discover Lingam Massage as a Private Rit…In Tips Why Your Drain Keeps Making Gurgling Noi…In Tips
Why Your Drain Keeps Making Gurgling Noi…In Tips Charter Bus Rental Illinois: Comfortable…In Travel
Charter Bus Rental Illinois: Comfortable…In Travel Why Dyno Data Matters in Picking Perform…In Automotive
Why Dyno Data Matters in Picking Perform…In Automotive Voozon Com Review: Is This Content Platf…In General
Voozon Com Review: Is This Content Platf…In General How to Use a Premium Calculator to Choos…In Insurance
How to Use a Premium Calculator to Choos…In Insurance











