TECHNOLOGICAL FADS TO LOOK OUT FOR ENHANCED CYBERSECURITY.The world is moving towards tremendous digital technology expansions. On the other side of the dark web are a series of sinister plots. They intend to threaten data integrity and privacy.
Companies world over are facing this dangerous problem of various cybercrimes. They lose out their essential trade secrets and other things amid aggravated competition.
Leading to:
- Mass public and regulatory authorities’ inconvenience,
- Steep fall in revenues,
- Reputational and image damage,
- Loss of clients/customers
- Losing revenues to competitors
- Loss of valuable time
- Damage to competitive edge elements
- Depreciation of authenticity and reliability
- Regulatory penalties, and
- Resource allocation for restoring operations, its integrity, and security features.
Many companies are also making new and better software of cybersecurity and controls. They aim to impede these threats. They further ensure the utmost privacy features into the computer and allied systems.
The compromise is there of data integrity and privacy. It is through an illegal entry into the cloud systems, mobile and wearable technology, Internet of things, etc.
Unethical Hackers and other cybercriminals often use Data centres, routers, and hosts points. They use as the primary source point of entry into the significant data breach, in the most sophisticated manner.
Cyber attackers are using strategies like:
- MiM attacks,
- Spying software
- Google glass
- Memory scraping malware
- Ransomware
- Malware
These are as a means to gain access to valuable information and insights.
An entrepreneur expansion of his business has to undertake the pressure of lack of funds.
Many new functions might have to be set up. It is along with equipping the business towards better cybersecurity systems, etc.
For this, make use of installment loans from a direct lender. It is a perfect idea for meeting all types of business expenditures.
All that the entrepreneur has to do is go online. He has to apply through the lender’s website, and the lending company will take care of the rest.
In a series of affordable instalment payments and interest rates, the pay the debt hassle-free.
LATEST TECHNOLOGICAL TRENDS FOR UPGRADING CYBERSECURITY
Below mentioned are some of the best ways to tackle cybersecurity breach problems:
VIRTUAL DISPERSIVE NETWORKING (VDN)
The idea of cybercriminals is to gain access to the extensive network itself. It achieves an advantage over its control.
To prevent a data breach in the networks, the communications split into various parts. They encrypt and route into varying independent protocol paths.
These paths are foolproof and legitimate. They are not enabling the hackers’ scope of their intrusion in any manner.
SAML AND THE CLOUD
Security assertion markup language (SAML) is a computer language. It is for exchanging data by using robust authentication and authorization features.
The level of data assurance and security gets reformed with this language combines with cloud systems.
SAML along with:
- Cloud
- SSO,
- Encryption and
- Intrusion detection technologies
They ensured the tracking of any nefarious movement in data or files and acted upon.
In this, no software needs to come into the installation. No changes are in need to make in end-user configurations.
Thus, it is a straightforward and convenient cybersecurity system. They enable timely alerts in the cloud platforms of any failed or unexpected logins, or other types of breach.
SAML + encryption technologies ensure to gain better control over internet and network traffic.
BEHAVIOURAL ANALYTICS
Behavioural Analytics is the latest trend in the types of cybersecurity measures.
It makes use of artificial intelligence, machine learning, blockchain technology, data mining, etc. It is to track unscrupulous data breach patterns.
Behavioural analytics aims to develop advanced data breach prevention security system. It is also to decipher any irregularity in the digital scheme of things.
For the same, behavioural analytics tracks the:
- Abnormal file movements
- Activity across target point of sale infrastructure
- Bioprinting
- Mobile Location tracking
- Profiling
- Third-party big data; and
- External threat intelligence
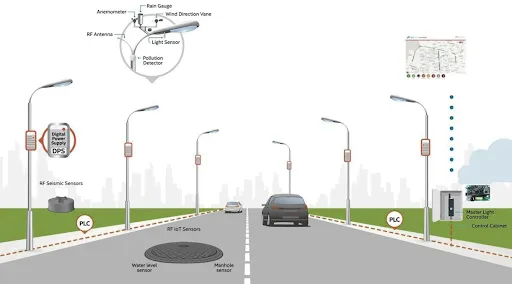
SMART GRID TECHNOLOGIES
Often, the field devices and meters become the first targets for cybercriminals. They tend to make use of as they are easy to compromise.
Smart grid technologies make sophisticated and high-end technologies of various types. They aim to sense and prevent any kind of cyber-attacks.
For this sensory, communications and control technologies are in practice to make:
- Padlock systems
- Watchdog systems
- SIEGate systems; and
- NetAPT systems
EMBEDDED HARDWARE AUTHENTICATION
It is a wholesome system of making use of both hardware and software. It comes to counter various cybersecurity threats.
In this, many authentication systems embed into a hardware device. It is through means of a computer chip for reliable detection and protection.
Series of authentication systems ensure that the hacker’s time gets lost. The test of patience is there to thwart the cyber-attack. Besides, it is to gain time for better data breach prevention measures.
ACTIVE DEFENSE MECHANISMS
The level of any cyber-attack through various means becomes aggressive and uncontrollable. It leads to huge data loss; the need for desperate and extreme measures comes into the forefront.
For this, the use of many novel methods is there as defence tactics to buy time or thwart the attack by making use of:
Cloaking identity: a cyber expert hides his original identity and gains data on cybercriminals for better preparation
Block malicious traffic: through better control over the whole network system along with hardware systems
Setup an isolated sole computer system that is left to become vulnerable for hackers and other cybercriminals to attack.
After this, measures of their ways and tactics of the data breach are studied extensively, and defence mechanisms are crafted.
This lone computer system also assists in recognizing spammers and catching hold of them.
These defence mechanisms are not reactive. They are proactive measures to thwart any sinister data breach plots through:
- Counterintelligence gathering
- Sink holing
- Honey pots
- Retaliatory hacking
- Reverse malware analysis
DESCRIPTION
Implemented updated and latest types of cybersecurity software and hardware will only ensure in retaining and maintaining data integrity and one’s privacy.
Hi, I am an Author who believes in making the life of their readers interesting with his writing. Writing was always my first interest. Ever since I was a teenager, I was already into writing poems and stories. Today, I have gained a great experience in my work. Check out my work and share your views.
Latest Articles
 Redefining Brand Trust With Online Reput…In General
Redefining Brand Trust With Online Reput…In General Ekart Partner Login System: Complete Gui…In Business
Ekart Partner Login System: Complete Gui…In Business Frankie Valli Net Worth, Early Life, Car…In Biography
Frankie Valli Net Worth, Early Life, Car…In Biography Erica Mena Net Worth, Early Life, Career…In Biography
Erica Mena Net Worth, Early Life, Career…In Biography Heading Abroad for Studies? Here’s Why a…In Education
Heading Abroad for Studies? Here’s Why a…In Education Teckjb com Explained: What It Is, How It…In Tips
Teckjb com Explained: What It Is, How It…In Tips The Reddit Breakthrough: Unlocking Front…In Technology
The Reddit Breakthrough: Unlocking Front…In Technology Top 10 Agencies in India Offering Strong…In General
Top 10 Agencies in India Offering Strong…In General